The Windows Registry 4
Categories of Data
Before putting data into the registry, an application should divide the data into two categories:
- Computer-specific data and
- User-specific data.
By making this distinction, an application can support multiple users, and yet locate user-specific data over a network and use that data in different locations, allowing location-independent user profile data. (A user profile is a set of configuration data saved for every user.) When the application is installed, it should record the computer-specific data under the HKEY_LOCAL_MACHINE key. In particular, it should create keys for the company name, product name, and version number, as shown in the following example:
HKEY_LOCAL_MACHINE\Software\MyCompany\MyProduct\1.0

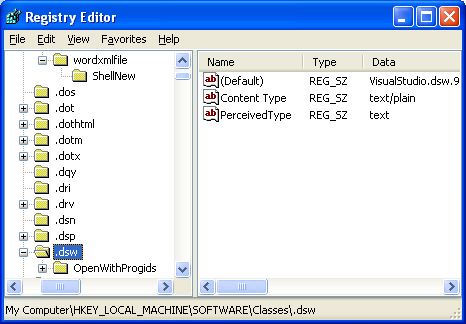
If the application supports COM, it should record that data under HKEY_LOCAL_MACHINE\Software\Classes.
An application should record user-specific data under the HKEY_CURRENT_USER key, as shown in the following example:
HKEY_CURRENT_USER\Software\MyCompany\MyProduct\1.0

Opening, Creating, and Closing Keys
Before an application can add data to the registry, it must create or open a key. To create or open a key, an application always refers to the key as a subkey of a currently open key. The following predefined keys are always open:
- HKEY_LOCAL_MACHINE,
- HKEY_CLASSES_ROOT,
- HKEY_USERS, and
- HKEY_CURRENT_USER
An application uses the RegOpenKeyEx() function to open a key and the RegCreateKeyEx() function to create a key. A registry tree can be 512 levels deep. You can create up to 32 levels at a time through a single registry API call. An application can use the RegCloseKey() function to close a key and write the data it contains into the registry. RegCloseKey() does not necessarily write the data to the registry before returning; it can take as much as several seconds for the cache to be flushed to the hard disk. If an application must explicitly write registry data to the hard disk, it can use the RegFlushKey() function. RegFlushKey(), however, uses many system resources and should be called only when absolutely necessary.
Writing and Deleting Registry Data
An application can use the RegSetValueEx() function to associate a value and its data with a key. To delete a value from a key, an application can use the RegDeleteValue() function. To delete a key, it can use the RegDeleteKey() function. A deleted key is not removed until the last handle to it has been closed. Subkeys and values cannot be created under a deleted key. It is not possible to lock a registry key during a write operation to synchronize access to the data. However, you can control access to a registry key using security attributes.
Retrieving Data from the Registry
To retrieve data from the registry, an application typically enumerates the subkeys of a key until it finds a particular one and then retrieves data from the value or values associated with it. An application can call the RegEnumKeyEx() function to enumerate the subkeys of a given key. To retrieve detailed data about a particular subkey, an application can call the RegQueryInfoKey() function. The RegGetKeySecurity() function retrieves a copy of the security descriptor protecting a key. An application can use the RegEnumValue() function to enumerate the values for a given key, and RegQueryValueEx() function to retrieve a particular value for a key. An application typically calls RegEnumValue() to determine the value names and then RegQueryValueEx() to retrieve the data for the names.
The RegQueryMultipleValues() function retrieves the type and data for a list of value names associated with an open registry key. This function is useful for dynamic key providers because it assures consistency of data by retrieving multiple values in an atomic operation. Because other applications can change the data in a registry value between the time your application can read a value and use it, you may need to ensure your application has the latest data. You can use the RegNotifyChangeKeyValue() function to notify the calling thread when there are changes to the attributes or contents of a registry key, or if the key is deleted. The function signals an event object to notify the caller. If the thread that calls RegNotifyChangeKeyValue() exits, the event is signaled and the monitoring of the registry key is stopped. You can control or specify what changes should be reported through the use of a notify filter or flag. Usually, changes are reported by signaling an event that you specify to the function. Note that the RegNotifyChangeKeyValue() function does not work with remote handles.
< Windows Registry 3 | Windows Registry Index | Win32 Programming | Windows Registry 5 >