Windows Access Control List (ACL) 12
Authorization Constants
Authorization constants are categorized according to usage as follows:
- Account Rights Constants.
- Privilege Constants.
- Account Rights Constants
Account rights, like privileges, determine the operations that a user account can perform. An administrator assigns account rights to user and group accounts. Each user's account rights include those granted to the user or to groups to which the user belongs. A system administrator can use the Local Security Authority (LSA) functions to work with account rights. The LsaAddAccountRights() and LsaRemoveAccountRights() functions add or remove account rights from an account. The LsaEnumerateAccountRights() function enumerates the account rights held by a specified account. The LsaEnumerateAccountsWithUserRight() function enumerates the accounts that hold a specified account right. All of the LSA functions mentioned above support both account rights and Privilege Constants. Unlike privileges, however, account rights are not supported by the LookupPrivilegeValue() and LookupPrivilegeName() functions. The GetTokenInformation() function will obtain information on account rights if TokenGroups, and not TokenPrivileges, is specified as the value of the TokenInformationClass parameter.
The following account right constants are used to control the logon ability of an account. The LogonUser() or LsaLogonUser() functions fail if the account being logged on does not have the account rights required for the type of logon being performed. The SE_DENY rights override the corresponding account rights. An administrator can assign an SE_DENY right to an account to override any logon rights that an account might have as a result of a group membership. For example, you could assign the SE_NETWORK_LOGON_NAME right to Everyone but assign the SE_DENY_NETWORK_LOGON_NAME right to Administrators to prevent remote administration of computers.
|
Account right constant |
Description |
|
SE_BATCH_LOGON_NAME |
Required for an account to log on using the batch logon type. |
|
SE_INTERACTIVE_LOGON_NAME |
Required for an account to log on using the interactive logon type. |
|
SE_NETWORK_LOGON_NAME |
Required for an account to log on using the network logon type. |
|
SE_SERVICE_LOGON_NAME |
Required for an account to log on using the service logon type. |
|
SE_DENY_BATCH_LOGON_NAME |
Explicitly denies an account the right to log on using the batch logon type. |
|
SE_DENY_INTERACTIVE_LOGON_NAME |
Explicitly denies an account the right to log on using the interactive logon type. |
|
SE_DENY_NETWORK_LOGON_NAME |
Explicitly denies an account the right to log on using the network logon type. |
|
SE_DENY_SERVICE_LOGON_NAME |
Explicitly denies an account the right to log on using the service logon type. |
|
Table 14 |
|
The preceding account right constants are defined as strings in ntsecapi.h. For example, the SE_INTERACTIVE_LOGON_NAME constant is defined as SeInteractiveLogonRight.
Privilege Constants
The following privilege constants are defined as strings in winnt.h. For example, the SE_AUDIT_NAME constant is defined as SeAuditPrivilege. The functions that get and adjust the privileges in an access token use the LUID type to identify privileges. Use the LookupPrivilegeValue() function to determine the LUID on the local system that corresponds to a privilege constant. You can use the LookupPrivilegeName() function to convert a LUID to its corresponding string constant. The operating system represents a privilege by using the string that follows User Right in the Description column of the following table.
|
Privilege constant/String |
Description |
|
SE_ASSIGNPRIMARYTOKEN_NAME SeAssignPrimaryTokenPrivilege |
Required to assign the primary token of a process. User Right: Replace a process-level token. |
|
SE_AUDIT_NAME SeAuditPrivilege |
Required to generate audit-log entries. Give this privilege to secure servers. User Right: Generate security audits. |
|
SE_BACKUP_NAME SeBackupPrivilege |
Required to perform backup operations. This privilege causes the system to grant all read access control to any file, regardless of the ACL specified for the file. Any access request other than read is still evaluated with the ACL. This privilege is required by the RegSaveKey() and RegSaveKeyEx() functions. The following access rights are granted if this privilege is held:
User Right: Back up files and directories. |
|
SE_CHANGE_NOTIFY_NAME SeChangeNotifyPrivilege |
Required to receive notifications of changes to files or directories. This privilege also causes the system to skip all traversal access checks. It is enabled by default for all users. User Right: Bypass traverse checking. |
|
SE_CREATE_GLOBAL_NAME SeCreateGlobalPrivilege |
Required to create named file mapping objects in the global namespace during Terminal Services sessions. This privilege is enabled by default for administrators, services, and the local system account. User Right: Create global objects. Windows XP, Windows 2000 SP3 and earlier, and Windows NT: This privilege is not supported. |
|
SE_CREATE_PAGEFILE_NAME SeCreatePagefilePrivilege |
Required to create a paging file. User Right: Create a pagefile. |
|
SE_CREATE_PERMANENT_NAME SeCreatePermanentPrivilege |
Required to create a permanent object. User Right: Create permanent shared objects. |
|
SE_CREATE_TOKEN_NAME SeCreateTokenPrivilege |
Required to create a primary token. User Right: Create a token object. |
|
SE_DEBUG_NAME SeDebugPrivilege |
Required to debug and adjust the memory of a process owned by another account. User Right: Debug programs. |
|
SE_ENABLE_DELEGATION_NAME SeEnableDelegationPrivilege |
Required to mark user and computer accounts as trusted for delegation. User Right: Enable computer and user accounts to be trusted for delegation. |
|
SE_IMPERSONATE_NAME SeImpersonatePrivilege |
Required to impersonate. User Right: Impersonate a client after authentication. Windows XP, Windows 2000 SP3 and earlier, and Windows NT: This privilege is not supported. |
|
SE_INC_BASE_PRIORITY_NAME SeIncreaseBasePriorityPrivilege |
Required to increase the base priority of a process. User Right: Increase scheduling priority. |
|
SE_INCREASE_QUOTA_NAME SeIncreaseQuotaPrivilege |
Required to increase the quota assigned to a process. User Right: Adjust memory quotas for a process. |
|
SE_LOAD_DRIVER_NAME SeLoadDriverPrivilege |
Required to load or unload a device driver. User Right: Load and unload device drivers. |
|
SE_LOCK_MEMORY_NAME SeLockMemoryPrivilege |
Required to lock physical pages in memory. User Right: Lock pages in memory. |
|
SE_MACHINE_ACCOUNT_NAME SeMachineAccountPrivilege |
Required to create a computer account. User Right: Add workstations to domain. |
|
SE_MANAGE_VOLUME_NAME SeManageVolumePrivilege |
Required to enable volume management privileges. User Right: Manage the files on a volume. |
|
SE_PROF_SINGLE_PROCESS_NAME |
Required to gather profiling information for a single process. User Right: Profile single process. |
|
SE_REMOTE_SHUTDOWN_NAME SeRemoteShutdownPrivilege |
Required to shut down a system using a network request. User Right: Force shutdown from a remote system. |
|
SE_RESTORE_NAME SeRestorePrivilege |
Required to perform restore operations. This privilege causes the system to grant all write access control to any file, regardless of the ACL specified for the file. Any access request other than write is still evaluated with the ACL. Additionally, this privilege enables you to set any valid user or group SID as the owner of a file. This privilege is required by the RegLoadKey() function. The following access rights are granted if this privilege is held:
User Right: Restore files and directories. |
|
SE_SECURITY_NAME SeSecurityPrivilege |
Required to perform a number of security-related functions, such as controlling and viewing audit messages. This privilege identifies its holder as a security operator. User Right: Manage auditing and security log. |
|
SE_SHUTDOWN_NAME SeShutdownPrivilege |
Required to shut down a local system. User Right: Shut down the system. |
|
SE_SYNC_AGENT_NAME SeSyncAgentPrivilege |
Required for a domain controller to use the LDAP directory synchronization services. This privilege enables the holder to read all objects and properties in the directory, regardless of the protection on the objects and properties. By default, it is assigned to the Administrator and LocalSystem accounts on domain controllers. User Right: Synchronize directory service data. |
|
SE_SYSTEM_ENVIRONMENT_NAME SeSystemEnvironment |
Required to modify the nonvolatile RAM of systems that use this type of memory to store configuration information. User Right: Modify firmware environment values. |
|
SE_SYSTEM_PROFILE_NAME SeSystemProfilePrivilege |
Required to gather profiling information for the entire system. User Right: Profile system performance. |
|
SE_SYSTEMTIME_NAME SeSystemtimePrivilege |
Required to modify the system time. User Right: Change the system time. |
|
SE_TAKE_OWNERSHIP_NAME SeTakeOwnershipPrivilege |
Required to take ownership of an object without being granted discretionary access. This privilege allows the owner value to be set only to those values that the holder may legitimately assign as the owner of an object. User Right: Take ownership of files or other objects. |
|
SE_TCB_NAME SeTcbPrivilege |
This privilege identifies its holder as part of the trusted computer base. Some trusted protected subsystems are granted this privilege. User Right: Act as part of the operating system. |
|
SE_UNDOCK_NAME SeUndockPrivilege |
Required to undock a laptop. User Right: Remove computer from docking station. |
|
SE_UNSOLICITED_INPUT_NAME SeUnsolicitedInputPrivilege |
Required to read unsolicited input from a terminal device. User Right: Not applicable. |
|
Table 15 |
|
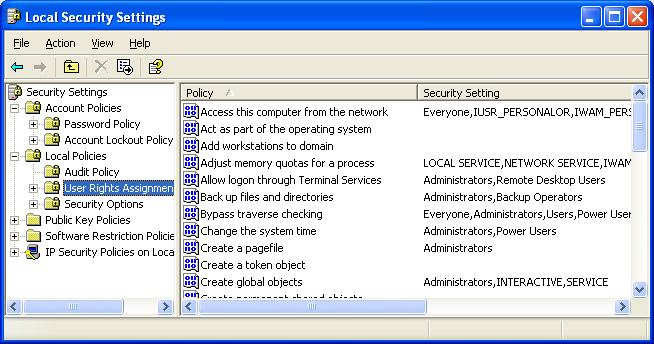
The operating system displays the user right strings in the Policy column of the User Rights Assignment node of the Local Security Settings Microsoft Management Console (MMC) snap-in as shown below (Administrative Tools → Local Security Policy).
The following code snippet shows how to enable or disable a privilege in an access token. The example calls the LookupPrivilegeValue() function to get the LUID that the local system uses to identify the privilege. Then the example calls the AdjustTokenPrivileges() function, which either enables or disables the privilege that depends on the value of the bEnablePrivilege parameter.
BOOL SetPrivilege(
HANDLE hToken, // access token handle
LPCTSTR lpszPrivilege, // name of privilege to enable/disable
BOOL bEnablePrivilege // to enable or disable privilege
)
{
TOKEN_PRIVILEGES tp;
LUID luid;
lpszPrivilege = LGenerate security audits;
if(!LookupPrivilegeValue(
NULL, // lookup privilege on local system
lpszPrivilege, // privilege to lookup
&luid)) // receives LUID of privilege
{
wprintf(LLookupPrivilegeValue() error: %u\n, GetLastError());
return FALSE;
}
tp.PrivilegeCount = 1;
tp.Privileges[0].Luid = luid;
if(bEnablePrivilege)
tp.Privileges[0].Attributes = SE_PRIVILEGE_ENABLED;
else
tp.Privileges[0].Attributes = 0;
// Enable the privilege or disable all privileges
if(!AdjustTokenPrivileges(
hToken,
FALSE,
&tp,
sizeof(TOKEN_PRIVILEGES),
(PTOKEN_PRIVILEGES) NULL,
(PDWORD) NULL))
{
wprintf(LAdjustTokenPrivileges() error: %u\n, GetLastError());
return FALSE;
}
if(GetLastError() == ERROR_NOT_ALL_ASSIGNED)
{
wprintf(LThe token does not have the specified privilege. \n);
return FALSE;
}
return TRUE;
}
We will explore the working program examples in other sessions later.
< Windows ACL 11 | Windows Access Control List (ACL) Main | Win32 Programming | Windows ACL 13 >